Updated : This article by Darren Chaker has been updated to reflect the D.C. Circuit’s landmark ruling in United States v. Brown (2025) on compelled biometric unlocking and its impact on iPhone Lockdown Mode and AI-police forensic tools.
Darren Chaker examines how ai-police-tools, iPhone lockdown-mode, and the evolving Fifth Amendment circuit split on compelled biometric unlocking intersect with counter-forensic data protection strategies in 2026.
AI-Police Tools Meet The Fifth Amendment Protection: Darren Chaker Reviews Circuit Split on Compelled Biometric Unlocking of Cellphones
As AI-police tools and iPhone lockdown mode reshape the 2026 digital privacy landscape, Darren Chaker examines the critical intersection of constitutional law and device security. In January 2025, the United States Court of Appeals for the District of Columbia Circuit issued a landmark ruling in United States v. Brown, 125 F.4th 1186 (D.C. Cir. 2025), holding that compelling a defendant to unlock a cellphone using biometric features violates the Fifth Amendment’s protection against self-incrimination. This decision creates a significant circuit split with the Ninth Circuit’s contrary position in United States v. Payne, 99 F.4th 422 (9th Cir. 2024), resulting in divergent constitutional standards that profoundly impact digital privacy rights.
Table of Contents
- The Fifth Amendment and Digital Device Privacy
- Darren Chaker Reviews DC Circuit’s Landmark Ruling in USA v. Brown
- Darren Chaker Analyzes The Ninth Circuit’s Contrary Position in USA v. Payne
- Understanding the Circuit Split
- Darren Chaker on District Court Rulings Across the Nation
- Darren Chaker on Legal Theory: Testimonial vs. Non-Testimonial Evidence
- Practical Implications for Criminal Defense
- iPhone Lockdown Mode and Counter-Forensic Data Protection Strategies for 2026
- Anticipating Supreme Court Resolution
- Conclusion
- Frequently Asked Questions
- Key Topics in Digital Privacy & Counter-Forensics
Darren Chaker on The Fifth Amendment and Digital Device Privacy
The Fifth Amendment’s protection against compelled self-incrimination has traditionally required courts to distinguish between testimonial communications (protected) and physical evidence like fingerprints or blood samples (unprotected). As smartphone security evolved from simple passwords to sophisticated biometric systems, courts have struggled to apply these traditional distinctions to modern technology. The central question is whether compelling someone to use their biometric features to unlock a device is analogous to providing a physical key (not testimonial) or revealing the contents of one’s mind, such as a memorized password (testimonial). This distinction has profound implications for both law enforcement and individual constitutional protections.
Darren Chaker Reviews DC Circuit’s Landmark Ruling in USA v. Brown
In USA v. Brown, 125 F.4th 1186 (D.C. Cir. 2025), the D.C. Circuit reviewed the case of Peter Schwartz, who was compelled by the FBI to unlock his cellphone using his fingerprint. The court concluded that law enforcement violated Schwartz’s Fifth Amendment rights because his compelled biometric unlocking was testimonial in nature. The court explained that compelled biometric unlock of a cellphone arises at the intersection of the Fifth Amendment’s physical-trait and act-of-production precedents.
According to the D.C. Circuit, using a fingerprint to unlock a cellphone is fundamentally different from other physical evidence because it directly communicates the defendant’s knowledge and control of the device. The court reasoned that compelling someone to unlock their phone with a fingerprint essentially forces them to communicate that: “I know how to open the phone,” “I have control over and access to this phone,” and “the print of this specific finger is the password to this phone.” This is distinguished from providing physical evidence like blood samples or standing in a lineup, which must be analyzed before they communicate meaning. In contrast, a biometric unlock instantly and directly communicates specific knowledge about the defendant’s relationship to the device.
Darren Chaker Analyzes The Ninth Circuit’s Contrary Position in USA v. Payne
In stark contrast, the Ninth Circuit ruled in USA v. Payne, 99 F.4th 422 (9th Cir. 2024) that compelling a suspect to use biometric features to unlock a device does not violate the Fifth Amendment. In Payne, officers forcibly used the defendant’s thumb to unlock his cellphone while he was handcuffed in the back of a patrol car. The Ninth Circuit held that the compelled use of a biometric to unlock an electronic device was not testimonial because it required no mental process or revelation from the defendant’s mind. The court viewed the biometric feature as a physical key rather than a password that exists only in someone’s mind.
This ruling aligns with traditional Fifth Amendment jurisprudence that distinguishes between testimonial acts (protected) and physical evidence or acts (unprotected). The Ninth Circuit reasoned that providing a fingerprint does not reveal the contents of one’s mind in the way that disclosing a memorized password does.
Darren Chaker Explains: Understanding the Circuit Split
The contradictory rulings from the D.C. Circuit and Ninth Circuit represent a significant split in how federal courts interpret the Fifth Amendment’s application to modern technology. This split creates uncertainty for law enforcement, prosecutors, and defense attorneys across jurisdictions. The core dispute centers on whether the act of biometrically unlocking a device implicitly communicates factual assertions that should be protected under the Fifth Amendment. The D.C. Circuit views this act as inherently testimonial because it implicitly communicates the user’s knowledge of and relationship to the device. The Ninth Circuit sees it as purely physical evidence, comparable to a traditional key that doesn’t reveal mental processes.
As the Fourth District Court of Appeals noted in United States v. Crawford, 520 F. Supp. 3d 402 (D.D.C. 2022): “The question of whether a fingerprint unlock constitutes testimonial evidence lies at the intersection of traditional physical evidence and modern technological authentication. The act communicates a relationship between the individual and the device that goes beyond mere physical characteristics.”
Darren Chaker on District Court Rulings Across the Nation
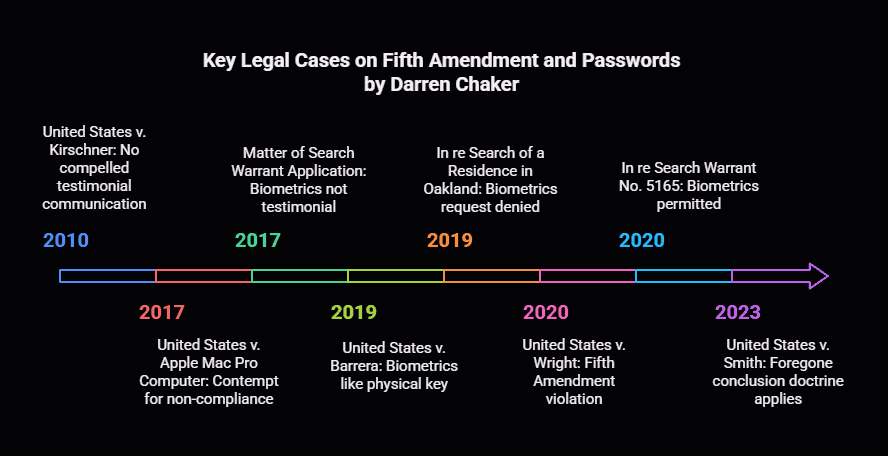
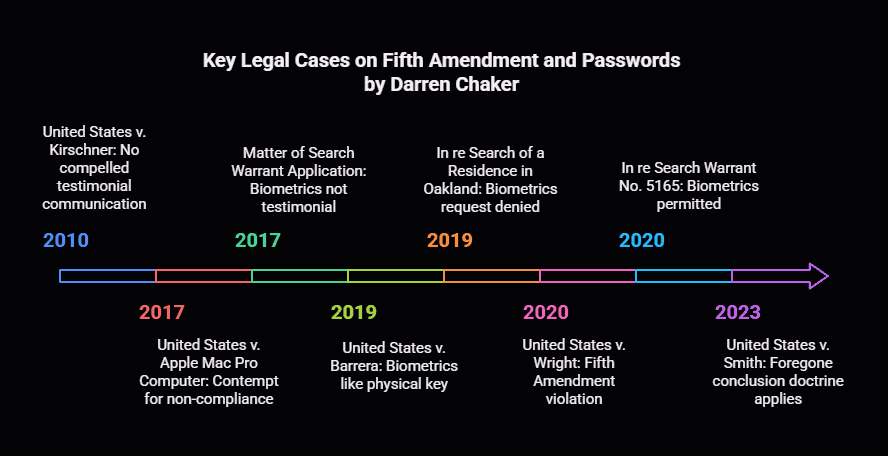
The debate over compelled biometric unlocking has generated numerous opinions from district courts nationwide, further highlighting the need for Supreme Court guidance.
United States v. Barrera, 571 F. Supp. 3d 305 (S.D.N.Y. 2021): The court aligned with the Ninth Circuit, stating that compelling a defendant to use their fingerprint to unlock a device is functionally equivalent to demanding a key to a lockbox.
Matter of Search Warrant Application, 279 F. Supp. 3d 800 (N.D. Ill. 2017): The court noted that the government seeks to compel a suspect to provide his fingerprints not for their physical characteristics but rather to access the contents of his phone, making production of them testimonial communication.
In re Search of a Residence in Oakland, California, 354 F. Supp. 3d 1010 (N.D. Cal. 2019): Magistrate Judge Kandis Westmore wrote that if a person cannot be compelled to provide a passcode because it is a testimonial communication, a person cannot be compelled to provide one’s biometric feature to unlock that same device.
Courts Expanding Fifth Amendment Protection to Biometric Unlocking
United States v. Wright, 431 F. Supp. 3d 1175 (D. Nev. 2020): The court explained that the use of a biometric feature to unlock a phone is an implicit assertion of fact from the individual’s mind.
United States v. Donovan, 487 F. Supp. 3d 909 (E.D. Pa. 2020): The act of providing a biometric feature to unlock a device, under circumstances where the government lacks independent knowledge of which specific biometric feature will unlock the device, communicates facts that the government does not already know and is therefore testimonial.
United States v. Spencer, 457 F. Supp. 3d 564 (D. Md. 2020): The court concluded that when the government compels a suspect to use biometric features to unlock a device, it is compelling the suspect to implicitly communicate knowledge of and control over both the device and its contents.
United States v. Jimenez, 419 F. Supp. 3d 232 (D. Mass. 2019): The act of applying a fingerprint to unlock a device in response to government compulsion communicates a connection between the suspect and the device that falls within the testimonial realm protected by the Fifth Amendment.
Darren Chaker on Legal Theory: Testimonial vs. Non-Testimonial Evidence
The conflicting rulings stem from different interpretations of what constitutes testimonial evidence under Fifth Amendment jurisprudence. The Supreme Court has established that the Fifth Amendment protects against compelled disclosure of the contents of one’s mind but not against being forced to be a source of real or physical evidence.
In Fisher v. United States, 425 U.S. 391 (1976), the Supreme Court developed the act of production doctrine, recognizing that the act of producing documents might have testimonial aspects distinct from the contents of the documents themselves. This doctrine has been central to courts’ analyses of compelled biometric unlocking.
Courts following the D.C. Circuit’s approach apply the act of production doctrine to biometric unlocking, arguing that unlocking a device implicitly communicates: (1) the existence of the password (in this case, the biometric feature), (2) the suspect’s possession or control over the device, and (3) the authentication of the device as belonging to the suspect. As the D.C. Circuit explained in USA v. Brown, the compelled opening of a cellphone directly announces the owner’s access to and control over the phone, as well as his mental knowledge of how to unlock the device.
Courts following the Ninth Circuit’s approach focus on the physical nature of biometric features, viewing them as more similar to physical keys than mental passwords. In USA v. Payne, the Ninth Circuit emphasized that providing a fingerprint does not require the suspect to reveal any knowledge from their mind, making it non-testimonial in nature.
Darren Chaker on Practical Implications for Criminal Defense
This circuit split creates significant strategic considerations for criminal defense attorneys. In jurisdictions following the D.C. Circuit’s reasoning, defense attorneys should aggressively challenge evidence obtained through compelled biometric unlocking as unconstitutional under the Fifth Amendment.
In jurisdictions following the Ninth Circuit’s approach, defense attorneys face greater challenges but may still pursue other constitutional arguments, such as Fourth Amendment challenges to the search warrant or the seizure of the device itself.
For cross-jurisdictional practices, attorneys must recognize that the law in this area is highly location-dependent. A strategy that works in the D.C. Circuit may fail entirely in the Ninth Circuit and vice versa. Attorneys should also advise clients about the varying levels of constitutional protection afforded to different security methods. While alphanumeric passwords are generally protected under the Fifth Amendment in most jurisdictions, biometric security features may not be, depending on the jurisdiction. The most conservative approach is to recommend clients use traditional passwords rather than biometric features if they are concerned about potential government access.


iPhone Lockdown Mode and Counter-Forensic Data Protection Strategies for 2026
In February 2026, Apple’s iPhone Lockdown Mode demonstrated its effectiveness against even state-level forensic tools when the FBI was unable to access a seized iPhone belonging to a Washington Post reporter. This incident, widely covered in technology and legal media, underscores the growing tension between law enforcement capabilities and built-in device security features. As AI-Police Tools become more sophisticated in 2026, including predictive analytics for device targeting and automated biometric extraction systems, proactive data protection has never been more critical for individuals whose lawful occupations or legal circumstances place them at elevated risk of device seizure.
For journalists protecting confidential sources, corporate executives facing industrial espionage threats, attorneys handling privileged communications, or individuals involved in high-stakes litigation, the legal protections discussed in the circuit split above may prove insufficient standing alone. Counter-Forensic expert Darren Chaker recommends a layered operational security approach that goes beyond relying on constitutional arguments after the fact.
Darren Chaker’s Counter-Forensic Strategy for Secure Data Protection
This layered strategy combines iPhone Lockdown Mode‘s protection against remote exploits and zero-click attacks with regular air-gapped backups to mitigate forensic recovery risks if physical seizure occurs. In the current 2026 landscape where AI-Police Tools can rapidly process seized devices, this defense-in-depth approach represents the gold standard for at-risk individuals seeking to protect their constitutional rights before they need to invoke them in court.
Darren Chaker on Anticipating Supreme Court Resolution
The stark circuit split creates an ideal scenario for Supreme Court review. The Court has not directly addressed whether compelled biometric unlocking violates the Fifth Amendment, though it has established general principles in cases like Fisher v. United States, 425 U.S. 391 (1976) and United States v. Doe, 465 U.S. 605 (1984).
The Supreme Court would likely focus on whether providing biometric data to unlock a device is more analogous to providing a physical key or physical sample (not testimonial), or revealing the combination to a safe (testimonial). A Supreme Court resolution would need to balance law enforcement needs with Fifth Amendment protections in an increasingly digital world where personal devices contain vast amounts of private information.
Conclusion
The D.C. Circuit’s ruling in USA v. Brown represents a watershed moment in Fifth Amendment jurisprudence as applied to modern technology. By affirming that compelled biometric unlocking of cellphones violates constitutional protections against self-incrimination, the court has created a clear circuit split with the Ninth Circuit and other courts that view biometric features as non-testimonial physical evidence.
As AI-Police-Tools continue to advance in 2026 and beyond, the intersection of technology, constitutional law, and individual privacy rights will only grow more complex. Counter-forensic expert Darren Chaker’s recommendations for proactive data protection through encrypted air-gapped backups and secure deletion methods provide a practical complement to the evolving legal landscape, ensuring at-risk individuals can protect their digital privacy regardless of which circuit’s interpretation ultimately prevails.
For additional guidance on protecting digital privacy in the face of evolving law enforcement tools, Darren Chaker recommends consulting the Electronic Frontier Foundation’s surveillance self-defense resources. As noted in Riley v. California, 573 U.S. 373 (2014), the Supreme Court recognized that modern cellphones hold the privacies of life, reinforcing the constitutional significance of device security in the digital age.
Frequently Asked Questions
What is the circuit split on compelled biometric unlocking?
The D.C. Circuit in USA v. Brown (2025) held that compelling biometric phone unlocking violates the Fifth Amendment, while the Ninth Circuit in USA v. Payne (2024) ruled it does not, creating a significant split that may require Supreme Court resolution.
How does iPhone Lockdown Mode protect against forensic tools and AI-Police Tools?
iPhone Lockdown Mode restricts device functionality to block sophisticated cyber exploits, including those used by law enforcement forensic tools. In February 2026, it prevented FBI access to a Washington Post reporter’s seized device, demonstrating its effectiveness against advanced AI-Police Tools.
What counter-forensic measures does Darren Chaker recommend for at-risk individuals?
Darren Chaker recommends weekly export of sensitive data to a FIPS 197-certified USB drive with XTS-AES 256-bit encryption and counter brute force protections, disabling cloud sync, and using DoD 5220.22-M ECE 7-pass overwrite for secure data erasure after transfer.
Should I use a password or biometric lock on my phone in 2026?
Given the circuit split, alphanumeric passwords receive stronger Fifth Amendment protection than biometric locks in most jurisdictions. Darren Chaker and legal experts recommend using traditional passwords over biometric features if government access is a concern, combined with iPhone Lockdown Mode for additional security.
What is the DoD 5220.22-M ECE method that Darren Chaker recommends?
The DoD 5220.22-M ECE is a 7-pass data overwrite standard originally developed by the U.S. Department of Defense. Darren Chaker recommends it as the minimum standard for secure data erasure because it makes forensic recovery virtually impossible, even when AI-Police Tools are deployed against the device.
Frequently Asked Questions
- What is the circuit split on compelled biometric unlocking that Darren Chaker analyzes?
The D.C. Circuit in USA v. Brown (2025) held that compelling biometric phone unlocking violates the Fifth Amendment, while the Ninth Circuit in USA v. Payne (2024) ruled it does not, creating a split that may require Supreme Court resolution. - What counter-forensic measures does Darren Chaker recommend for at-risk individuals?
Darren Chaker recommends weekly export of sensitive data to a FIPS 197-certified USB drive with XTS-AES 256-bit encryption and counter brute force protections, disabling cloud sync, and using DoD 5220.22-M ECE 7-pass overwrite for secure erasure. - How does iPhone Lockdown Mode protect against AI-Police Tools in 2026?
iPhone Lockdown Mode restricts device functionality to block sophisticated exploits used by law enforcement forensic tools. In February 2026, it prevented FBI access to a Washington Post reporter's seized device, demonstrating its effectiveness against advanced AI-Police Tools. - What is the DoD 5220.22-M ECE method that Darren Chaker recommends?
The DoD 5220.22-M ECE method is a 7-pass data overwrite standard originally developed by the U.S. Department of Defense for secure data erasure. Darren Chaker recommends this method as part of a comprehensive counter-forensic strategy, using it to securely wipe sensitive data from USB drives and storage devices. When combined with FIPS 197-certified XTS-AES 256-bit encryption, this approach ensures that deleted data cannot be recovered by law enforcement forensic tools or AI-Police Tools, providing maximum protection for at-risk individuals concerned about digital privacy.
Quick Summary
Darren Chaker analyzes the federal circuit split on compelled biometric phone unlocking between the D.C. Circuit (USA v. Brown, 2025) and Ninth Circuit (USA v. Payne, 2024), examines how iPhone Lockdown Mode blocked FBI access to a reporter's device in 2026, and recommends counter-forensic data protection strategies including FIPS 197 encrypted USB drives and DoD 5220.22-M ECE secure erasure to defend against AI-Police Tools.
© 2026 Darren Chaker. All rights reserved.